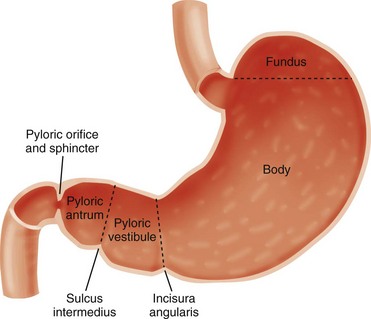
Chapter 101 Hypertrophic pyloric stenosis (HPS) is the most common surgical entity affecting infants during the first 6 months of life.1 It has an incidence of approximately 2 to 5 per 1000 births among children of European descent, but its incidence is much lower in other populations—approximately 0.7 per 1000 births among children of African American or Asian extraction. The preponderance among male infants is well known, variably cited as 2.5 to 5.5 : 1.2 Its incidence is inversely proportional to birth order, with odds ratio to birth order cited as 1, 2, 3, 4+ being roughly equivalent to increased risk levels of 1.9, 1.5, 1.3, and 1.0.3 The condition demonstrates a familial predisposition, suggesting a polygenic inheritance with greater penetrance in males; thus among children of affected fathers, the risk is approximately 5% for sons and 2.5% for daughters, whereas among children of affected mothers, the corresponding risk is 20% for boys and 7% for daughters. Proband concordance in monozygotic twins is cited as between 0.25 and 0.44, whereas in dizygotic twins it is reduced to 0.05 to 0.10, which is very similar to that of nontwin siblings.3 Hirschsprung originally described the entity postmortem in two patients4 and incorrectly assumed that HPS is congenital. Although some exceptions may exist, as discussed later in this chapter, data indicate that HPS is not present at birth, and its symptoms and characteristic anatomic changes typically present between 3 and 12 weeks of age. Rollins et al.5 examined 1400 neonates who had normal ultrasound findings at birth; HPS later developed in nine of these subjects. These findings and others lend credence to the belief that the disease evolves over a course of days to weeks.6–8 Occasional case reports indicate that the diagnosis of HPS is made earlier in life, but documentary proof often is incomplete.9 The stomach is divided by the incisura angularis into the body and fundus proximally and the antrum distally. The latter is further subdivided by the sulcus intermedius into a pyloric vestibule proximally and a pyloric antrum or pyloric canal distally, which is approximately 2.5 cm in length and terminates at the pyloric sphincter and orifice, which lead into the duodenum10 (Fig. 101-1). In infants with HPS, the pyloric antrum is no longer distensible and therefore is no longer clearly demarcated from the pyloric sphincter. The entire complex presents as one elongated canal with thickened muscular walls and filled with edematous mucosa. The thickened muscular walls are unable to relax, thus preventing the normal distensibility of the canal, and the lumen is obstructed by redundant, thickened, and hyperemic folds of mucosa (Fig. 101-2, A and B).6,11,12 Figure 101-2 Histopathologic anatomy. Although the diagnosis and surgical treatment of HPS have undergone a remarkable evolution during the past century, its cause remains unknown. The final common pathway seems to be one of work hypertrophy of the circular muscle of the pylorus, as if it were under constant stimulation, and it becomes unable to relax; the mucosa also becomes edematous and hypertrophied, sometimes markedly, simulating a polypoid mass.13,14 Because of a lack of an obvious etiologic agent or process, associated findings have been linked to etiology—for example, to a paucity of omentum (likely due to emaciation) and to “higher development of the nervous system” in children of the “intellectual classes”18 in the eighteenth and early twentieth centuries. More recently, attention has centered on the hypertrophied muscle. The thickened muscle is depleted of inhibitory peptides (such as vasoactive polypeptide); synaptic vesicles, presynaptic terminals, and neural cell adhesion molecules; markers for enteric glia; interstitial cell of Cajal; and nitric oxide synthetase activity at the messenger ribonucleic acid level, with increases in insulin-like and platelet-derived growth factors. Immunoreactivity studies evaluating desmin content suggest immaturity of the intermediate filaments in the hypertrophied pyloric muscle.19–29 The mucosa is thickened and edematous, and both muscle and mucosa are hyperemic when evaluated with color and spectral Doppler imaging.6,13 Despite the extensive anatomic and biochemical changes documented in persons with HPS, as early as 4 months after surgery, the anatomic changes and assays for nerve growth factor, interstitial cells of Cajal, and nitric oxide synthase activity revert to normal.27,30 Prostaglandin E2 generation in the gastric mucosa and increased concentration in the gastric secretions of patients with HPS have been reported.31 Prostaglandin E1 and E2 have been reported to induce proliferation of gastric mucosa32 and are related to muscle contraction in the human gastrointestinal tract23; prostaglandin therapy has preceded the development of HPS requiring surgery.33 The macrolide antibiotic erythromycin is a prokinetic agent and has been associated with increased risk of developing HPS in some series, particularly when the infants are exposed very early in life; however, further studies have determined that the link, if it exists, is weak and the potential risk is very small.3 More recently, genetic susceptibility loci have been identified, including chromosomes 16p12-p13 and 11q14-q22 and genes encoding neuronal nitric oxide synthase on chromosome 12q.15–17 Babies with HPS typically present with a history of forceful nonbilious vomiting, often described as “projectile,” that may be relatively sudden in onset or preceded by initially mild symptoms consistent with gastroesophageal reflux. If the diagnosis is not made promptly, protracted vomiting leads to dehydration and to the development of hypochloremic metabolic alkalosis, with paradoxical aciduria as renal mechanisms designed to maintain intravascular volume supervene, conserving sodium at the expense of hydrogen ions. Starvation can exacerbate the effect of the diminished hepatic glucuronyl transferase activity, leading to indirect hyperbilirubinemia in a small number of infants. In patients who present after significant weight loss and who are thin and dehydrated, peristaltic waves may be seen on the wall of the scaphoid abdomen, progressing from the left upper quadrant across the epigastrium, flanked by a protuberant rib cage.11 Currently, most infants present earlier, with less severe physical findings and laboratory abnormalities. Investigators have emphasized the changing pattern of presentation of infants with HPS; most infants presenting today do not have evidence of metabolic abnormalities, and it has been suggested that the increased availability of ultrasound may be a factor in earlier diagnosis.34–36 Physical examination in experienced hands often is diagnostic through palpation of the “olive” or “pyloric tumor,” terms often used to designate the tactile findings in persons with HPS. This examination requires a calm infant and a committed examiner willing to dedicate 15 minutes or longer to the examination, which may require decompression of the overdistended stomach via a nasogastric tube.37 If the olive is palpable, the examination is diagnostic. The sensitivity of abdominal palpation varies with the experience of the examiner and ranges between 24% and 99%; specificity ranges between 92% and 99%.37–41 False-positive results do occur and have been reported to be as high as 14%, with anatomic variants such as unusual extensions of the left lobe of the liver and congenital abnormalities such as malrotation and duplication cysts.42,43 The documented accuracy of ultrasound diagnosis has generated a trend toward reliance on imaging rather than on the potentially more protracted physical examination. Although the loss of clinical skills may be lamentable in some respects, and some persons have argued that imaging increases the financial cost of the workup of HPS, other investigators have recognized that, despite “fading skills,” the rapidity and accuracy of ultrasound diagnosis can result in “better patients,” that is, better surgical candidates at the time of diagnosis.34,35 Plain radiographs may strongly suggest the diagnosis, revealing a markedly distended stomach, particularly if several peristaltic waves are seen, with little gas distally (Fig. 101-3),44 although absence of these findings does not negate the diagnosis. In rare instances, HPS has been reported in association with isolated gastric pneumatosis that resolves after the stomach is decompressed (e-Fig. 101-4).45 Figure 101-3 An abdominal radiograph in an infant with pyloric stenosis. e-Figure 101-4 Gastric pneumatosis in an infant with pyloric stenosis. In addition to a delay in the passage of contrast material from the stomach, several other radiographic signs are present in infants with HPS. The pyloric channel is narrowed, and as contrast material begins to enter the narrowed channel, it may appear as a “beak” that evolves into a “string” or a “double tract” sign as contrast material courses between the interstices of the luminal mucosa, compressed by the thickened, unrelaxing antropyloric muscle, which typically is curved upward and posteriorly (Fig. 101-5). The enlarged muscle mass encroaches upon the lumen of the antrum proximally, resulting in the “shoulder sign”; when the duodenal base is also deformed by the thickened muscle, the appearance may resemble an “apple core” lesion. The “pyloric tit” occasionally can be seen along the lesser curve just proximal to the impression of the pyloric mass; it represents contrast material trapped within the lumen of the stomach, compressed between a peristaltic wave and the impression of the pyloric muscle upon the adjacent, more distal portion of the stomach. Virtually all of the aforementioned signs can be seen transiently in most infants. The study should document the persistence of the findings to ensure the diagnosis of HPS. Figure 101-5 Upper gastrointestinal series in patients with pyloric stenosis. Ultrasound was first applied to the diagnosis of HPS in five cases described in 1977 utilizing B-mode sonography.46 Since that time, ultrasound has become the modality of choice in the diagnosis of HPS in most pediatric centers and is considered the “gold standard” by many investigators.11,35,37 Unlike the upper GI test, this examination does not require contrast material to traverse the obstructed canal for diagnosis, and thus the diagnosis can be made quickly, without the need for additional distension of the stomach and without radiation exposure to the infant, which can be prolonged in infants with a high degree of obstruction.
Hypertrophic Pyloric Stenosis
Overview
Anatomy
Abnormal
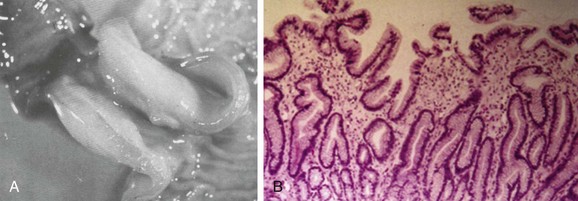
A, A gross postmortem specimen of hypertrophied pylorus in an infant who succumbed to this condition. Note the thickened muscle and the thickened mucosa, which would fill and obstruct the lumen of the unsectioned antropyloric canal. B, A histologic specimen of antropyloric mucosa in an infant with pyloric stenosis with typical presentation, operative findings, and postoperative recovery. The hematoxylin and eosin stain shows mucosal hyperplasia with elongated, branched, and mildly distorted pits and abundant edematous lamina propria.
Etiology
Clinical Presentation
Diagnosis and Imaging
Radiographic Studies
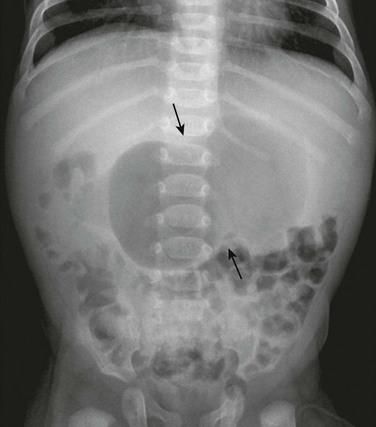
An abdominal radiograph demonstrates a distended stomach with a peristaltic wave (arrows), with normal to mildly decreased distal gas. In the appropriate clinical setting, these findings are highly suggestive of pyloric stenosis.
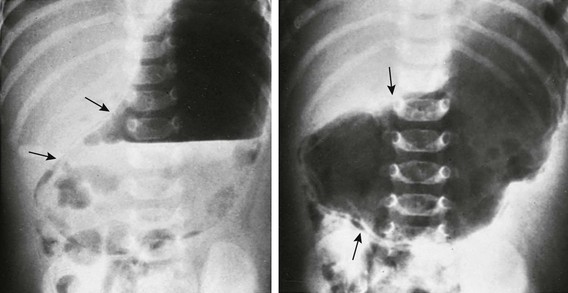
Supine abdominal radiographs in a 6-week-old girl with pyloric stenosis shows a markedly dilated stomach with several peristaltic waves and decreased distal gas. Intramural gas is present (arrows), which resolved within 24 hours after decompression with gastric intubation. (Courtesy Dr J. Leonidas, New Hyde Park, NY.)
Upper Gastrointestinal Series
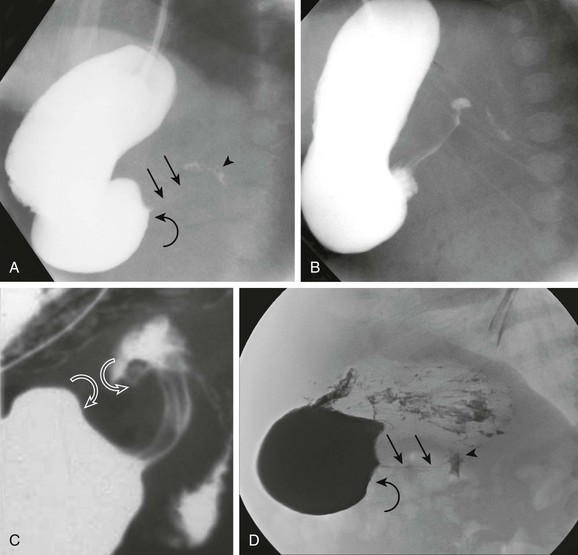
A, An orogastric tube was used to evacuate the stomach, and barium was instilled under fluoroscopic control. The image shows a peristaltic wave and a small amount of contrast entering the narrowed canal, demonstrating both a beak (curved arrow) and string sign (straight arrows). The arrowhead points to the duodenal bulb. B, Shortly after the image shown in part A, additional contrast material egressed into the pyloric channel, now outlining a double tract proximally. C, An oblique radiograph in another infant with pyloric stenosis shows mass impression upon the proximal antrum and the distal duodenal base (curved arrows), spanned by the upwardly and posteriorly directed antropyloric canal with three contrast tracts coursing through the intraluminal mucosal folds. D, An oblique radiograph of the same infant shown in Fig. 101-8, C. Curved arrows point to the mass impression of the pyloric muscle on the gastric antrum, or “shoulder sign.”
Ultrasonography
![]()
Stay updated, free articles. Join our Telegram channel

Full access? Get Clinical Tree

Hypertrophic Pyloric Stenosis